- Huawei Mate 60 Pro Makes Satellite Calls: Only US$0.18/minute
- Huawei Mate60 Pro: First Smart Phone Supports Satellite Calls
- 14000 cores + 450W: RTX 4080 graphics card perfectly replaces the RTX 3080
- Big upgrade: The difference between Bluetooth 5.0 and 5.2
- Geeks Disappointed that RTX 4080/4090 doesn’t come with PCIe 5.0
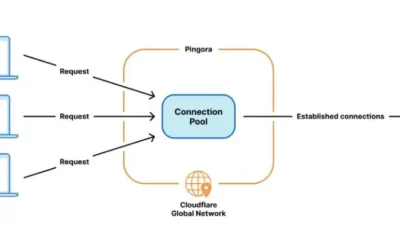
- What are advantages and disadvantages of different load balancing?
Soft router refers to the use of desktop or server with software to form a routing solution, mainly relying on software settings to achieve the function of the router;
while hard routing is a unique hardware device, including processor, power supply, embedded software, providing Router function set.
 According to the different operations used, it can be divided into software routers based on windows platform and Linux/bsd platform.
According to the different operations used, it can be divided into software routers based on windows platform and Linux/bsd platform.
The more common software firewalls based on Windows platform are ISA Server, Winroute Firewall, Xiaocao Internet behavior management soft router, etc.
Some of these software are commercialized, and usually charge differently according to the number of authorized users.
The cost of purchasing a genuine software firewall is undoubtedly a big expense for many small and medium-sized enterprises, and software firewalls based on Unix/Linux platforms Software firewalls are constantly being introduced.
Most of these software firewalls are free. Common ones include:
The common feature of these systems is that they generally have low hardware requirements, and even only need a computer, a hard disk, and two network cards to install a very professional software firewall.
This is for many people who have eliminated low-end computers. That means to take an obsolete computer, install a set of free firewall software, and DIY a professional firewall.
Such a system itself also includes NAT functionality and enables broadband sharing.
In other words, this free firewall is actually an excellent broadband router, which is very exciting.
But such free soft routing is usually for survival or to cause dissatisfied users due to excessive advertising.
Features of soft Routering
1. Powerful firewall function:
Support two to seven layers of firewall rules, real-time monitoring of abnormal network behavior, timely detection and timely prohibition.
2. Effective bandwidth management:
Optimize the network, allocate network bandwidth reasonably, effectively prevent network congestion, and ensure smooth network transmission as much as possible.
3. Email security:
Email backup, email antivirus, and spam filtering ensure the safety of external contacts.
4. Effectively resist various cyber threats:
Effectively manage the online behaviors of Internet users, formulate corresponding access strategies, reduce the security risks faced by the network, and ensure the security of the network.
5. Multiple access methods:
Multiple access methods such as routing, gateway, and parallel connection reduce the impact on the network.
Without changing the network environment, it is convenient to realize the management of the original network.
6. Avoid legal risks:
Effectively shield illegal websites and block the illegal surfing behaviour of Internet users.
7. Friendly management interface:
The easy-to-use WEB way of management can realize management and control without installing any client software.
8. Improve work efficiency:
Control some people’s online chat, games and other behaviors to improve work efficiency.
9. Reduce network management costs:
Existing hardware can be used. It also supports functions such as gateways, firewalls, routers, IDS, content monitoring, etc., which can fully meet the general network security and management needs without purchasing other network security equipment.
Effectively solve the contradiction of small and medium-sized network users on the one hand for network security and network management, on the other hand, they cannot invest too much in purchasing expensive various professional equipment. Using RedCat NSS is free.
Function of soft routing
1. Operating platform: WindowsXP, Windows2003, Windows Vista, Windows2008, Windows7.
2. Designed for high-end applications, supporting the need to go online from dozens of machines to thousands of machines at the same time.
3. Support bandwidth consolidation and load balancing of up to 127 external network outlet lines. Support single network card to realize multi-outlet NAT, which can realize bandwidth superposition.
4. The world’s first object-oriented full 3D operation interface (any ordinary graphics card can be used), intuitively display the Internet status of all machines.
5. Anti-ARP attack, flood DDOS attack, etc. No client installation is required.
6. Intelligent bandwidth allocation, which can dynamically allocate bandwidth according to the number of Internet machines and bandwidth conditions. 2MADSL can support 15-20 machines to surf the Internet at the same time.
Advantages and disadvantages of soft routing
Advantages:
1. Good price controllability:
The soft router usually uses an ordinary computer to act as, the computer can be from a very old PC to an advanced PC/serial server, and the configuration cost is controlled according to user needs.
If you configure an ordinary linux router, it can be achieved by using a second-hand computer with poor performance.
To achieve a large amount of equipment and more functions, you can also add better hardware equipment according to user needs.
2. Multi-purpose:
The second advantage of using soft routing is that the purchased machine will not be wasted, because the soft routing itself is a computer, even if it is not needed to configure the soft routing in the future, it can also be used for other purposes.
And because the hardware router is a dedicated device, it can be said to be dedicated for a special fee.
3. Flexible function selection:
Different software routers can provide different functions, such as PPP/PPPOE dial-up Internet access and management software, NAT network address forwarding function, IPFW interconnection protocol firewall management program, DHCP dynamic IP configuration protocol program and management software, DNS, VPN virtual private Common functions such as network, HTTP and FTP services, web authentication, traffic restriction, and restriction of illegal broadband users to surf the Internet can all be implemented on the soft router, which is very flexible and convenient.
For hard routers, each device has a specific function.
Although different products provide different functions, as long as one of them is selected, the selected router function is basically fixed.
You cannot add or delete arbitrarily. You can only choose to open or restrict the use of a certain part of the function.
Of course, the current hardware router manufacturers generally completely concentrate the functions in a router product, and customers can use it according to their own needs.
Disadvantages:
1. Complex configuration:
A good soft router, such as RouterOS, is developed by a foreign organization and used as a router system.
The software itself is relatively good, but because it is developed abroad, its software is based on the English interface and the configuration is quite complicated.
RouterOS There are so many configuration parameters, the complexity and the full English configuration interface is far from an ordinary user.
Professional technicians also need to refer to the configuration manual when configuring the soft router.
Even with the help of the manual, they cannot fully control it, and can only try and explore continuously by themselves.
2. Too much power consumption:
PC is a power-hungry thing, and mainstream PCs are about 250-400W per hour.
The monthly power consumption of a computer: if it is 300W per hour × 24 hours a day × 30 days a month = 216KW, that is, 216 kWh, then a year is 2592 kWh.
If there is a monitor, plus the monitor (80-100W/h), then the money spent on electricity bills every year is considerable.
3. The hardware is not stable enough:
As we all know, the PC architecture is designed for personal use. In all respects, it is not suitable for the role of a server in harsh environments.
A PC and various accessories are produced by different manufacturers, although they are based on certain Standardized production, but its compatibility is not necessarily guaranteed.
Even if it is experienced personnel equipped with a relatively perfect PC, how about its performance?
The owner of an Internet cafe, as a person who uses computers every day, should know the most in his heart. Basically, PCs are not able to adapt to the ability to work 24 hours a day, 365 days a year, otherwise, what are the servers doing?
The user directly buys a high-end PC to be the server, isn’t it more cost-effective? Not to mention that many soft routers use old hosts, and their performance is problematic.
4. Software update is not timely:
Since the excellent soft routing vendors are basically foreign, and the domestic network environment changes, they cannot perceive it in time.
It is often that a problem has occurred for a long time before there are corresponding update measures, such as viruses, attacks, etc. , And many customers are even using free versions or pirated versions, and they cannot get timely support from manufacturers.
This is determined by the soft routing system.
- DIY a PBX (Phone System) on Raspberry Pi
- How to host multiple websites on Raspberry Pi 3/4?
- A Free Intercom/Paging system with Raspberry pi and old Android phones
- DIY project: How to use Raspberry Pi to build DNS server?
- Raspberry Pi project : How to use Raspberry Pi to build git server?